Support Developer Speed, Maintain Organizational Execution
Individual developer efficiency has surged by over 70%, thanks to AI copilots and agents. Yet organizational efficiency delivering production-ready solutions remains below 15%.
To address this gap, 79% of organizations have either mostly or fully standardized internal developer platforms (IDPs) to scale AI safely, repeatably, and with governance that holds up under scrutiny.
Perforce provides the automation engine that makes your internal developer platform (IDP) run, bringing order to development chaos. Remove friction from the software delivery lifecycle and empower your developers to move faster with less risk.

The DevOps Tech Stack for Platform Engineers
Modern developers are moving faster than ever, but the systems supporting them are not optimized.
Perforce accelerates internal developer platform adoption and automation with our DevOps tech stack, helping platform engineering teams:
Accelerate Time to Market
Shorten lead times from idea to production.
Improve Developer Experience
Minimize cognitive load and reduce developer burnout.
Ensure Security and Compliance
Enforce consistent security checks and compliance controls automatically.
Your Tech Stack, Our Automation Solutions
Perforce integrates seamlessly within your internal developer platform to enable an end-to-end automated flow. We provide the core capabilities your platform engineering team needs to enforce security, increase system reliability, and accelerate digital quality.
- Infrastructure & Configuration: Automate and manage your infrastructure consistently to prevent configuration drift.
- Compliant Data Delivery: Eliminate data bottlenecks. Refresh test data in minutes, not weeks, without violating compliance rules.
- API Governance: Centralize enforcement and policy management to stop API chaos across teams.
- Open Source Governance: Secure enterprise-grade support for over 400 open-source technologies, ensuring clear ownership and security patch assurance.
Assured Governance & Risk Management With ISO 42001 Certification
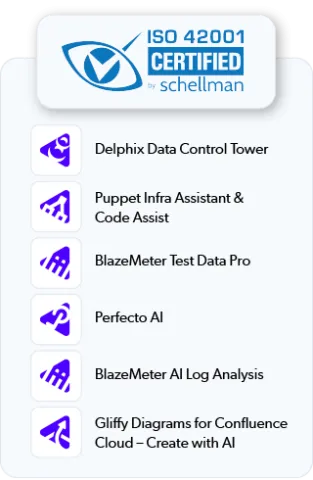
Perforce is proud that several of our AI products and features hold ISO 42001 certification. This achievement demonstrates our commitment to the highest standards of information security and environmental sustainability. This globally recognized certification ensures that our processes and systems comply with stringent international requirements for managing data securely while minimizing environmental impact.
With these ISO 42001 certifications, these Perforce solutions assure customers of robust governance, risk management, and sustainable AI practices, reinforcing trust and accountability in every interaction. This certification underscores our dedication to delivering secure and environmentally responsible solutions, setting the benchmark for excellence in the technology sector.

Customer Success: Modernizing Infrastructure at Scale
TransUrban needed to manage a massive API ecosystem securely while modernizing over 100,000 road-tech assets. They adopted Perforce to accelerate digital integration, ensure compliance, and improve developer productivity through streamlined onboarding.
The Results:
3-year ROI with a 6-month payback period.
faster test environment creation.
more masked and protected data environments.
additional revenue generated from improved developer productivity.
Achieve Continuous Delivery Without Trade-Offs in Quality, Security, or Control
Enterprise software delivery can no longer afford to be slow, fragmented, or fragile. Build a shared, scalable, and secure Internal Developer Platform that standardizes workflows and enables true self-service for your developers.
