Increase IP Reuse and Reduce Re-spins
In today’s market, acceleration requires IP reuse. But without a centralized system to manage IP, hardware teams are left searching for or recreating designs, and software engineers end up tracking versions on a spreadsheet. These manual processes waste time and increase the risk of errors and unnecessary re-spins. Perforce IPLM provides a scalable IP lifecycle management platform that tracks IP and its metadata across projects, providing end-to-end traceability and enabling effortless IP reuse. Learn more by connecting with an IP expert today.
IP-Centric Features Semiconductor Teams Need
Key benefits of Perforce IPLM
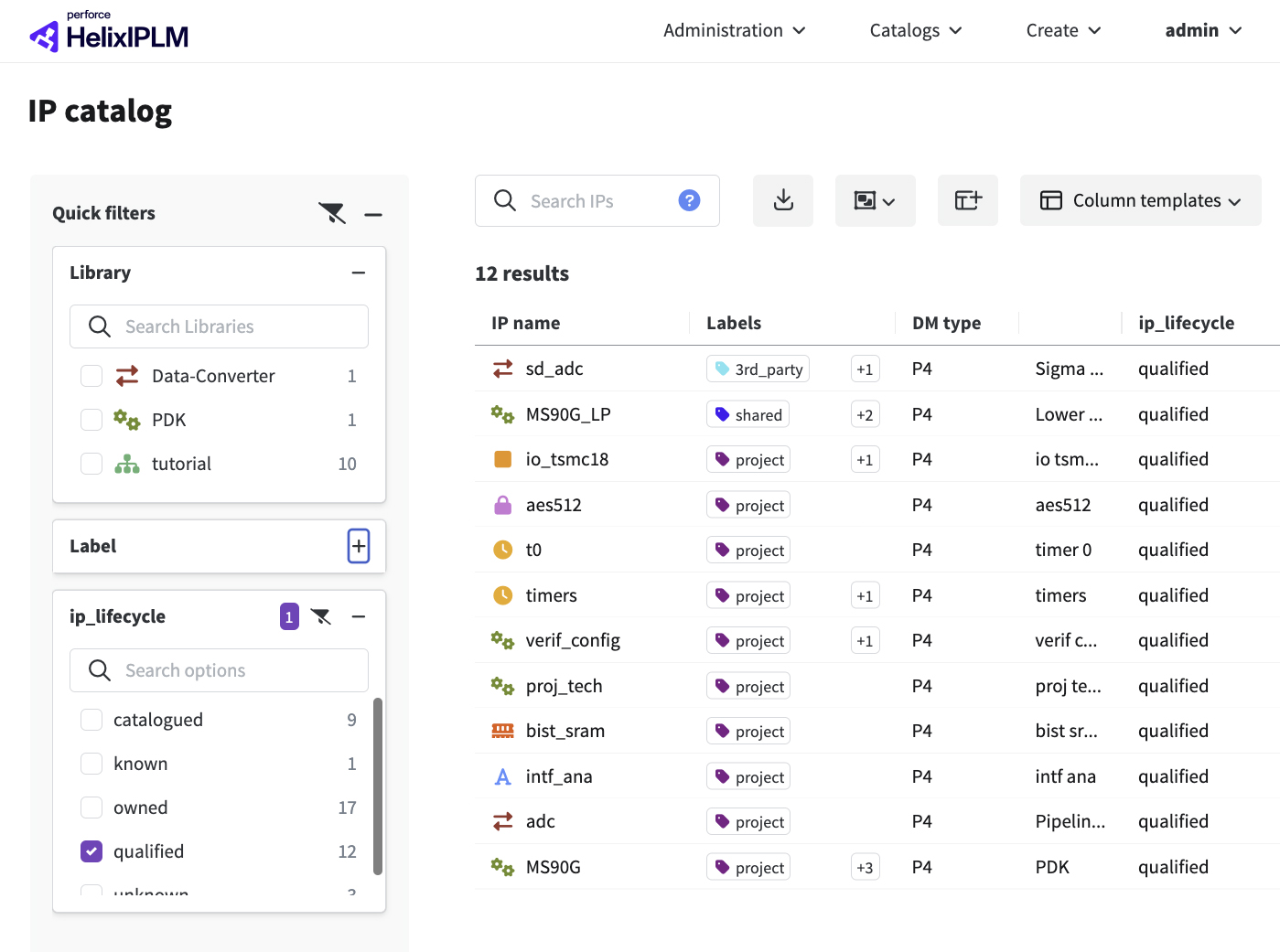
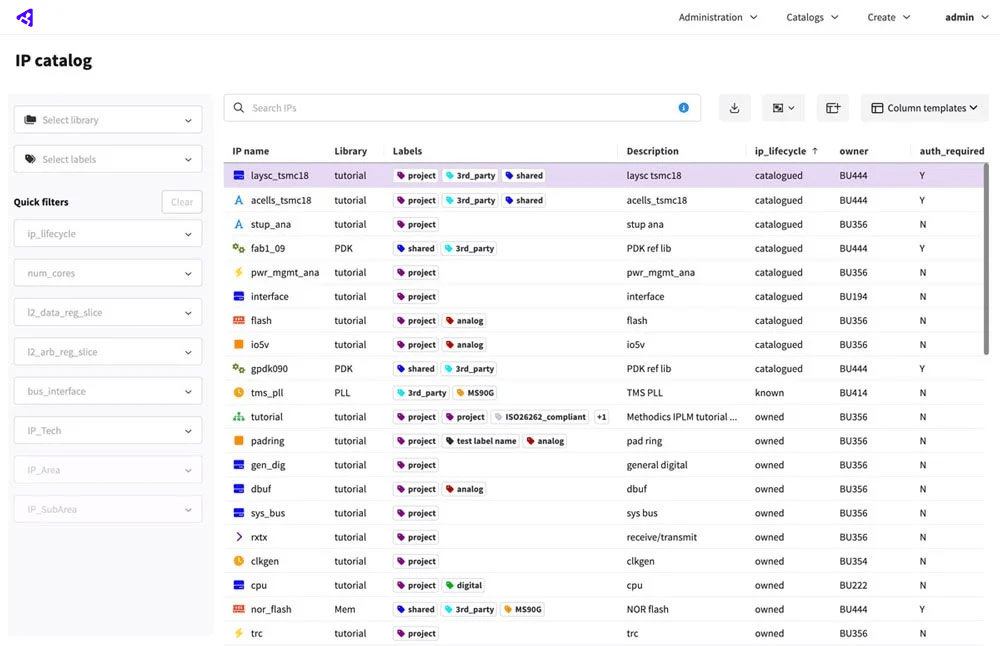
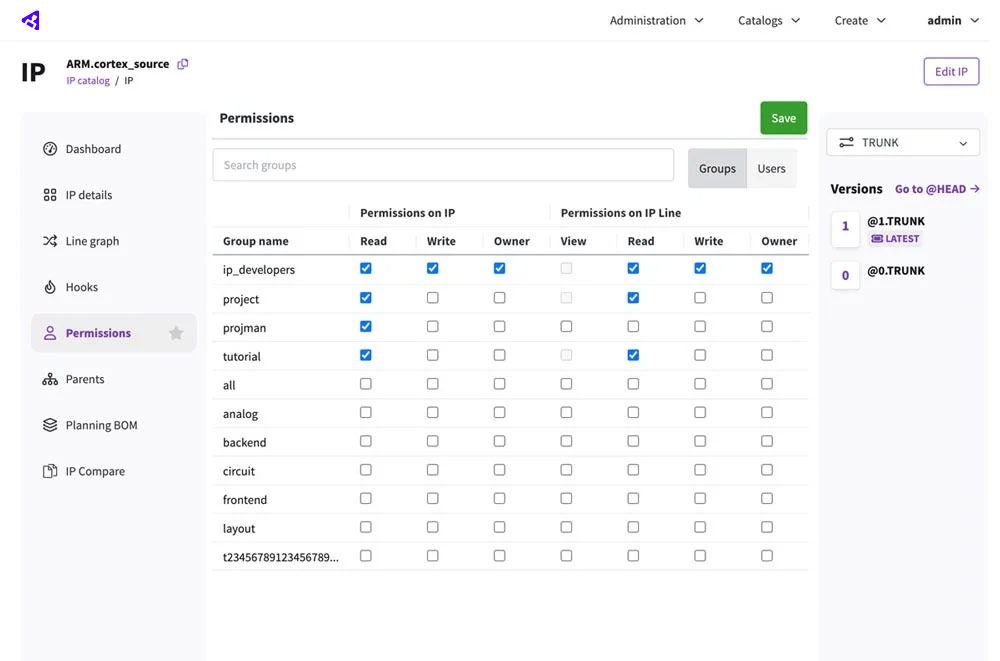
Perforce IPLM provides an integrated IP catalog with powerful search and filtering capabilities. This allows designers to quickly and easily find the IP they need. And fine-grained permissions ensure they can only access the IP that is available to them. Every aspect of the IP lifecycle is tracked and visible in IPLM in easy-to-understand, configurable dashboards. Designers can see the projects the IP has been used in, any outstanding bugs, derivative designs, regression status, and much more.
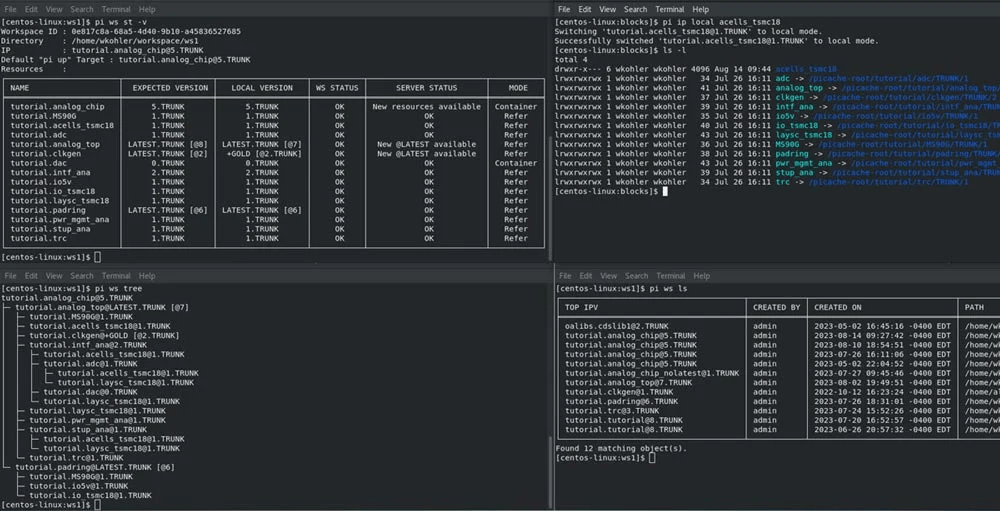
Workspaces are central to SoC integration. It’s the point where IP and the rest of the design come together. IPLM's advanced IP and data caching infrastructure reduces workspace creation time from hours to seconds — and dramatically decreases data storage requirements. So designers have instant access to the files and data they need.
Administrators can track IP usage and development across the enterprise. And comprehensive controls enable admins to determine the design files, IPs, tool configurations, machine resource allocation, and other infrastructure components available to team members.
See the Workspace Demo
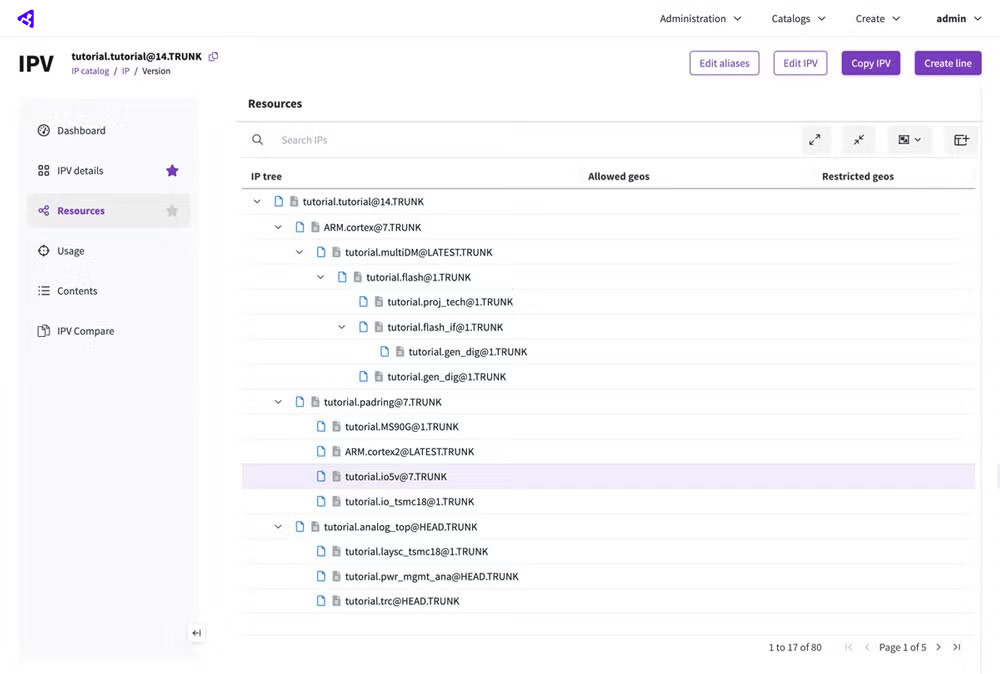
IPLM provides a single source of truth for creating and managing your bill of materials (BoM). With a hierarchical BoM for hardware, software, and the platform, you get a complete view of the project, including all versions and dependencies. These versioned releases ensure quality through centralized management of IP integration rules and checkpoints. For example, you can define which range of hardware IP versions a software component is compatible with. So, if a hardware team upgrades, IPLM will flag a compatibility mismatch. Teams can even integrate planned and in-progress IPs in a Planning BoM to accelerate the design planning process and enable better build-or-buy decisions.
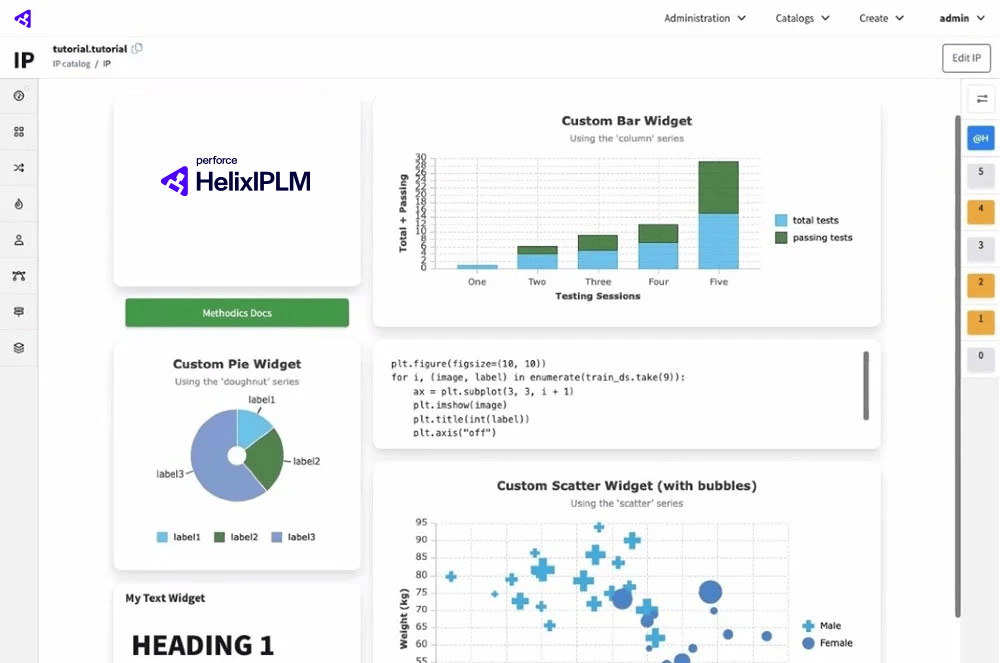
Data is key to making informed project decisions. IPLM offers at-a-glance visibility of data through configurable dashboards, backed by a powerful data analytics platform. Default dashboard configurations are provided for common design tasks, such as IP qualification, IP release status, and IP usage information. And new widgets can easily be added through the user-friendly, visual widget editor. IPLM also includes a first-class RESTful API for custom dashboard development, including company specific reporting, industry compliance, or integration of existing corporate systems.
See Dashboards in the Demo
IPLM automates the design release process, eliminating the risks associated with manually releasing a design. Hierarchical release mechanisms ensure that IP blocks are released in the correct order, based on design dependencies, for quality-driven release flows. IPLM also provides pre-release and post-release hooks and triggers to ensure no IPs are made available to others until they meet your organization's standards for IP Quality and maturity.
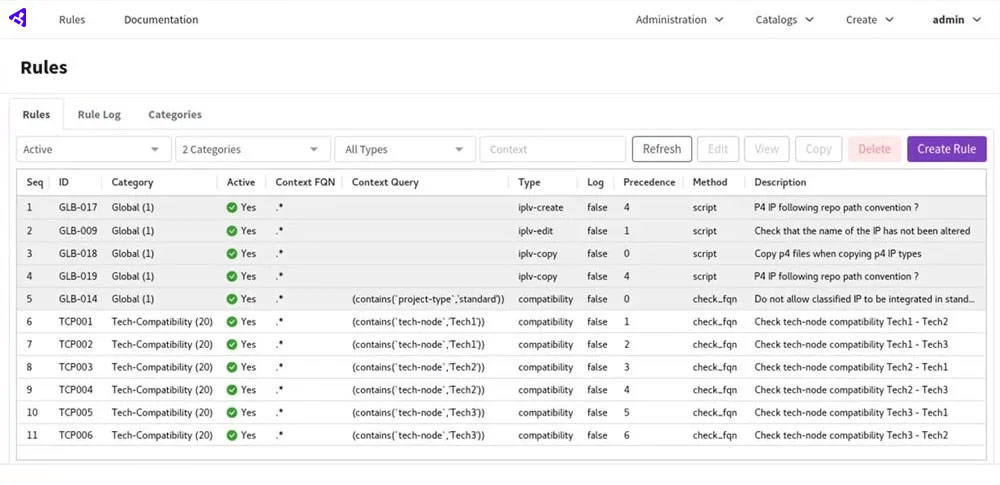
IPLM ensures the highest level of security to protect critical IP assets from every angle. Fine-grained user permissions allow you to control IP access. And with end-to-end traceability from requirements to release, you can easily track IP usage across your entire IP catalog — and quickly identify vulnerabilities in released ICs. Violating technology export control laws can result in millions of dollars in fines, on top of lost revenue and market setbacks caused by IP leakage. IPLM’s Geofencing feature ensures compliance and prevents IP leakage by restricting IPs and metadata in prohibited locations, regardless of access permissions.
9/10 Top Semiconductor Companies Use Perforce
The world’s best semiconductor companies trust Perforce to accelerate design, improve collaboration, and speed time to market.
Monthly User Group
Join our monthly session with IPLM experts and other users for open discussion, Q&A, and product demos.
A Day in the Life: Design Engineer
What could you do with the hours it takes to locate the right IP — or the months it takes to recreate it when you can’t? See how Perforce P4 (formerly Helix Core) and IPLM enable design reuse, streamline the design process, and ensure quality.
Talk to an Expert
Our experts can review your current environment and help your organization scale to the next level.
Join the User Group
Join the monthly session with IPLM experts and users for open discussion, Q&A, and product demos.